For over a decade, Security Operations Centers (SOCs) have been built incrementally. A SIEM here, an IAM there, a SOAR added later, plus niche tools for identity, endpoints, cloud, and compliance. On paper, this modular approach looked flexible. In practice, it has created brittle security architectures that struggle under real-world pressure.
Today’s attacks exploit exactly what stitched-together SOCs fail at: speed, context, and accountability.
How SOCs Evolved Incorrectly
Most SOCs did not emerge from a single architectural vision. They evolved reactively.
A breach led to a new tool.
A compliance mandate added another layer.
A cloud migration introduced yet another console.
Over time, SOCs became collections of loosely connected products, each optimized for its own domain but blind to the full picture. Detection lives in one place, identity context in another, response somewhere else, and risk reporting in spreadsheets.
This evolution assumed that integration could compensate for fragmentation. That assumption no longer holds.
Integration Debt as a Hidden Risk
Integration debt is the security equivalent of technical debt, invisible until things break.
Every connector between SIEM, IAM, SOAR, UEBA, PAM, and NAC introduces latency, failure points, and semantic gaps. Alerts may flow, but meaning does not. Identity signals lose richness. Risk scores get flattened. Response actions depend on brittle playbooks.
When tools are integrated after the fact, no system truly owns the incident lifecycle. Data arrives late, context is incomplete, and automation hesitates when decisiveness matters most.
In modern attacks, especially identity-driven ones, milliseconds and context decide outcomes.
When Fragmented SOCs Fail: Real-World Security Crises
Over the past two years, multiple large-scale cyber incidents have revealed a consistent weakness in enterprise security operations. These were not failures caused by outdated tools or underfunded SOCs. In most cases, organizations had modern SIEMs, IAM platforms, and response tooling in place. What failed was the stitched-together SOC model itself, one where detection, identity context, and response were distributed across disconnected systems with no single point of ownership.
The following incidents illustrate how fragmentation, rather than capability gaps, turned security events into full-blown crises.
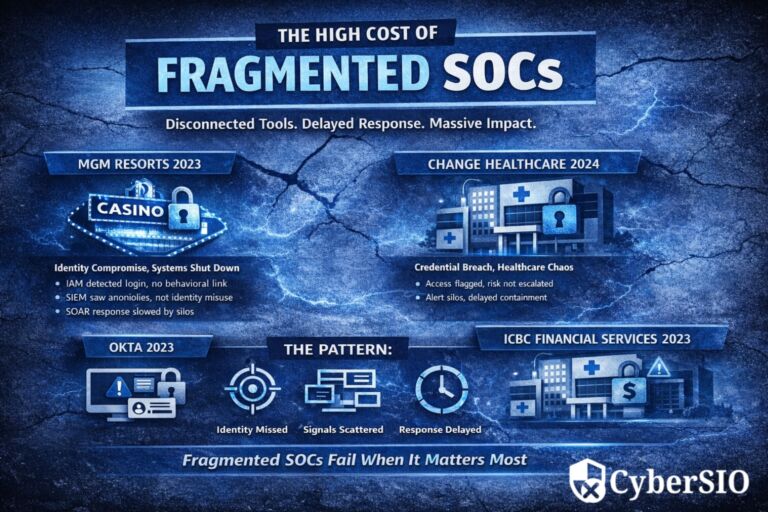
MGM Resorts International – Identity Compromise Leading to Operational
Shutdown
In 2023, MGM Resorts experienced a major operational disruption after attackers exploited helpdesk processes to compromise identity access. Once inside, the attackers moved laterally and disabled critical systems across casinos, hotels, and customer services.
While identity activity and anomalous behavior were logged, the SOC struggled to respond decisively because signals were split across identity systems, monitoring tools, and response platforms.
Where fragmentation contributed to failure
· Identity events were detected, but not evaluated as high-risk threats
· Behavioral anomalies lacked direct linkage to access enforcement
· Response actions required manual coordination across teams
· No unified system owned identity misuse from detection to containment
Change Healthcare – Credential Compromise Escalating to National Disruption
In early 2024, Change Healthcare suffered a ransomware incident that disrupted healthcare
payments and services across the United States. The initial access stemmed from compromised credentials, despite existing identity and security controls.
The breach escalated because identity risk, lateral movement and operational impact were handled by separate systems and teams. Security signals existed, but they were not correlated quickly enough to trigger decisive response.
Where fragmentation contributed to failure
· IAM logged access, but lacked continuous risk evaluation
· SOC tools detected anomalies without identity context
· Response ownership was split between security, identity, and IT teams
· Delayed containment allowed operational damage to spread
Okta – Session Visibility Gaps in SOC
Operations
In 2023, Okta disclosed a compromise involving its customer support systems. While core identity infrastructure was not directly breached, attackers accessed session-related data that could be used for account takeover attempts.
This incident exposed a critical blind spot common in fragmented SOCs: session behavior is often monitored separately from authentication
and identity threat detection.
Where fragmentation contributed to failure
· Authentication logs existed without session-level behavior correlation
· Session risk signals were not treated as SOC-critical events
· Downstream customers lacked unified visibility into exposure
· Response depended on post-incident reconstruction rather than real-time action
ICBC Financial Services – Cyber
Incident Becoming a Systemic Event
In 2023, a ransomware attack on ICBC Financial Services disrupted U.S. Treasury trade settlements, demonstrating how SOC fragmentation can amplify impact beyond a single organization.
Security detection, IT operations, and business continuity teams operated in silos, slowing coordinated response and escalating operational fallout.
Where fragmentation contributed to failure
· Security and operational monitoring were not unified
· Business impact was assessed after, not during, the incident
· Response decisions lacked a single authoritative control plane
· Cyber risk translated directly into systemic financial disruption
A Repeating Pattern Across Incidents
Across these events, the failure pattern is consistent:
· Identity was the primary attack vector, but secondary in SOC design
· Signals existed, but context was fragmented across tools
· Response capabilities were present, but accountability was unclear
· Time was lost stitching together answers instead of stopping attacks
These incidents demonstrate that stitched-together SOCs do not fail because they lack tools. They fail because they lack architectural unity.
This realization is driving a fundamental shift toward unified SOC models, where threat, identity, and risk operate as a single, accountable system.
Why Accountability Matters During Incidents
In a fragmented SOC, accountability is diffused.
When an incident unfolds, teams ask:
- Was this detected by SIEM or UEBA?
- Should IAM have blocked this login?
- Did SOAR fail to trigger the playbook?
- Who owns the final decision to contain?
This ambiguity delays action. Worse, it complicates post-incident forensics and regulatory reporting. Without a single system owning detection-to-response, enterprises struggle to prove who knew what, and when.
Accountability is not a process issue, it is an architectural one.
Potential Loss from Integration-Dependent SOCs and Lack of Accountability
The cost of stitched SOCs is not theoretical.
Operationally, SOC teams burn time correlating alerts manually, increasing mean time to respond. Strategically,
leadership lacks confidence in risk posture because signals are scattered and inconsistent. Financially, breaches escalate because identity misuse, lateral movement, or privilege abuse is detected too late.
In regulated sectors, the impact extends further. Incomplete audit trails, delayed incident reporting, and unclear ownership can translate into fines, reputational damage, and executive liability.
Integration-dependent SOCs do not fail loudly. They fail quietly, until the damage is done

Introduction to Unified SOC Thinking
Unified SOC thinking starts with a simple premise: detection, context, and response must be native to the same operational fabric. Instead of integrating silos, a unified SOC is designed as a single system where threat, identity, and risk signals are correlated at the core. Identity is not enrichment, it is foundational. Automation is not an add-on, it is inherent. Risk is not a report, it is continuously evaluated. This approach reduces complexity not by removing capabilities, but by removing fragmentation.Why a Unified SOC Keeps Enterprise Security Fortified
A unified SOC changes how security teams operate.Identity signals are correlated in real time with behavior, access, and privilege. Threats are understood in context, not as isolated events. Response actions execute with confidence because they are driven by a shared data model, not brittle integrations.
For analysts, this means fewer false positives and faster decisions. For CISOs, it means clearer accountability and measurable risk reduction. For enterprises, it means resilience against attacks that no longer rely on malware alone, but on abusing trust and identity.
Unified SOCs are not just more efficient. They are structurally better aligned to modern attack realities.CyberSIO Unified SOC-in-a-Box: Threat, Identity, and Risk in One Platform
The Unified SOC-in-a-Box approach brings threat management, identity threat detection, and risk governance into a single operational platform. Instead of stitching together SIEM, SOAR, IAM, UEBA, PAM, and NAC, these capabilities operate as one system. Identity signals drive detection. Risk scoring prioritizes response. Automation enforces containment. Compliance and reporting are generated as a byproduct of operations, not an afterthought. This model restores what stitched SOCs lost: clarity, speed, and ownership. As enterprises confront identity-first attacks, disinformation-driven breaches, and regulatory pressure, the question is no longer whether integration works. The question is whether the SOC itself is architected for accountability.Unified SOCs answer that question by design.

