Introduction
In today’s hyperconnected digital environment, cyber threats are no longer limited to malware, ransomware, or network breaches. A new class of attacks is rapidly emerging, disinformation campaigns, deepfake fraud, and large-scale impersonation operations that target trust, identity, and reputation.
As highlighted in CyberSIO’s use case overview, disinformation is no longer just a media or content moderation issue, it has become a full-scale security threat vector affecting access, operations, and governance. For enterprises, governments, and critical infrastructure operators,
disinformation security and deepfake detection are now strategic imperatives. This blog explores why influence-based threats matter, how they impact organizations, and how CyberSIO enables enterprises to respond effectively.
Understanding Disinformation and Deepfake Threats
What Is Disinformation?
Disinformation refers to the intentional creation and spread of false or misleading information to manipulate perceptions, behaviors, and decisions. In enterprise environments, this includes:
- Fake news targeting brands or leadership
- Coordinated social media manipulation
- False crisis narratives
- Market and investor misinformation
According to CyberSIO’s brochure, many of these campaigns ultimately lead to identity takeovers, fraudulent access, and insider risks rather than just reputational damage.
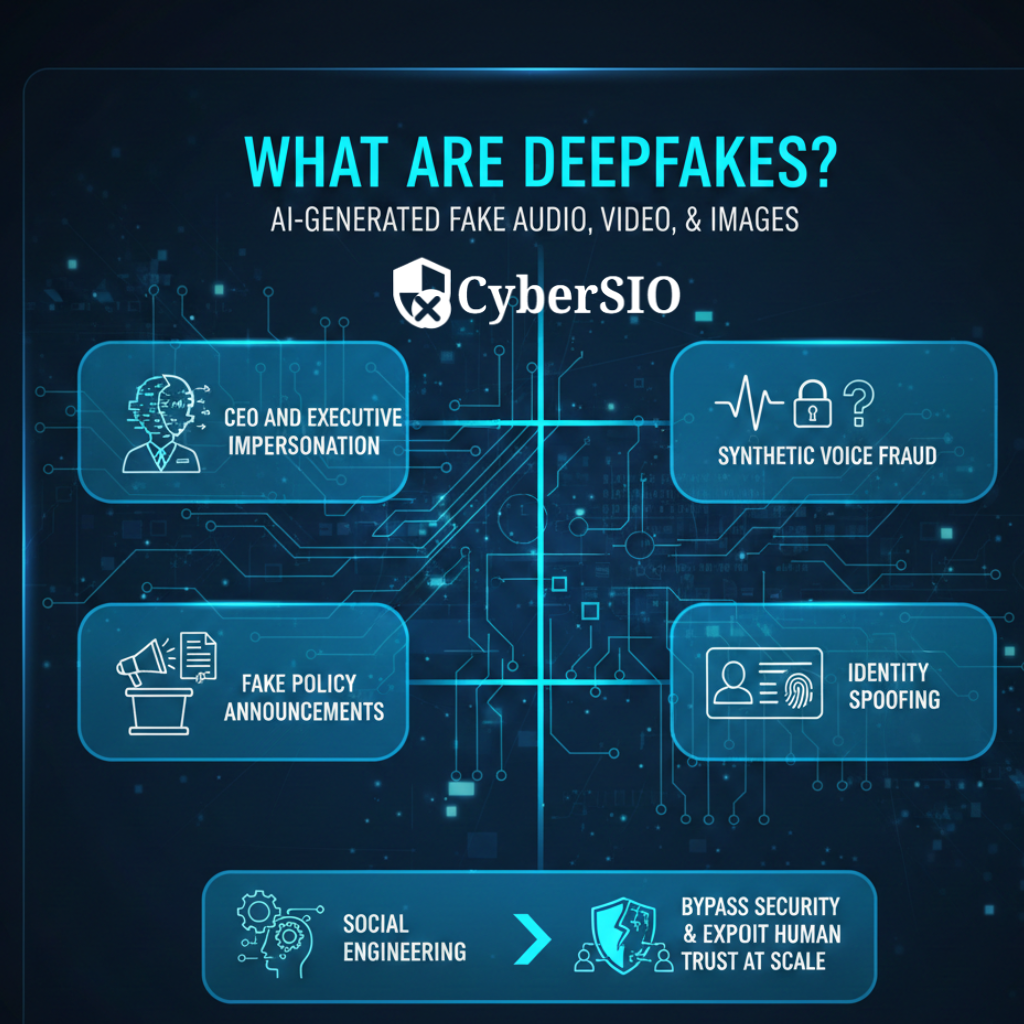
What Are Deepfakes?
Deepfakes
use artificial intelligence to generate realistic fake audio, video, and images. These are increasingly used for:
- CEO and executive impersonation
- Synthetic voice fraud
- Fake policy announcements
- Identity spoofing
When combined with social engineering, deepfakes bypass traditional security controls and exploit human trust at scale.
Why Traditional Cybersecurity Tools Fall Short
Conventional security platforms focus on technical indicators such as malware signatures, network anomalies, and endpoint behavior. However, narrative-driven and identity-based attacks operate outside these boundaries.
Key limitations include:
- Limited monitoring of social and media ecosystems
- No correlation between narrative signals and access systems
- Lack of identity-context awareness
- Inability to operationalize reputational threats
As noted in CyberSIO’s documentation, most IAM, SIEM, and SOAR platforms do not recognize synthetic or narrative inputs unless external signals are integrated. This results in delayed detection and reactive response.
Business Impact of Disinformation and Deepfake Attacks
Unmanaged influence-based threats can create cascading risks across organizations:
Financial Impact
- Fund transfer fraud
- Fake investment schemes
- Payment redirection attacks
Reputational Damage
- Loss of public trust
- Brand dilution
- Market credibility erosion
Regulatory and Compliance Exposure
- Reporting failures
- Audit complications
- Legal liabilities
Operational Disruption
- Panic-driven incidents
- Service interruptions
- Policy confusion
Executive and Leadership Risk
- Targeted impersonation
- BEC attacks
- Insider manipulation
These risks are especially critical in BFSI, government, and infrastructure sectors.
Disinformation Security: A Core Cyber Capability
Disinformation security treats narrative manipulation and impersonation as security incidents rather than communication challenges.
CyberSIO positions this capability as a “cybersecurity response layer” for trust-based attacks, enabling systems to react using identity, automation, and access controls.
Key elements include:
- Continuous narrative monitoring
- Detection of coordinated campaigns
- Threat actor attribution
- Trust-impact risk scoring
- SOC workflow integration
This approach embeds influence-risk management into core security operations.
Deepfake Detection and Impersonation Defense
Effective protection requires both technical and contextual intelligence.
Technical Detection
- AI-based media forensics
- Voice and facial biometrics
- Metadata analysis
- Media authenticity validation
Contextual Validation
- Identity behavior analytics
- Privilege and access correlation
- Transaction pattern monitoring
- Executive communication verification
CyberSIO’s ITDR platform detects abnormal identity behavior arising from synthetic personas and impersonation, enabling early intervention
Integrating Narrative Intelligence into the SOC
Modern organizations are embedding narrative intelligence into Security Operations Centers to achieve unified visibility.
According to CyberSIO’s solution architecture, upstream tools such as deepfake detectors and narrative intelligence platforms feed signals into the SOC through standardized APIs .
Integrated SOC capabilities include:
- Real-time impersonation monitoring
- SIEM signal enrichment
- SOAR-driven response automation
- Risk-based prioritization
- Forensic and audit support
This transforms disinformation into measurable and actionable security events.
Industry Use Cases
BFSI
In a typical scenario, a deepfake CEO voice is used to authorize fund transfers. CyberSIO’s ITDR detects approval anomalies, IAM enforces re-authentication, and SOAR freezes funds while triggering legal workflows .
Key use cases:
- CEO fraud prevention
- Synthetic identity detection
- Compliance-driven response
Government and PSU
Fake circulars or impersonated officials can trigger policy confusion and public distrust. CyberSIO enables:
- Identity verification
- Communication lockdowns
- Crisis coordination
- Regulatory audit trails
Critical Infrastructure and Energy
Coordinated misinformation campaigns can cause panic and operational disruption. CyberSIO integrates narrative AI signals into SOC dashboards and automates alerts to leadership and authorities .
Large Enterprises and Brands
- Executive impersonation defense
- Fake domain and profile detection
- Brand abuse monitoring
- Insider risk mitigation
CyberSIO’s Role in Disinformation Security and Deepfake Detection
CyberSIO does not compete with narrative AI or media authenticity platforms. Instead, it specializes in connecting trust-risk signals to enterprise security systems, making them actionable .
CyberSIO as the Security “Nerve Center”
CyberSIO acts as the orchestration layer that translates disinformation signals into security responses by:
- Correlating narrative risks with identity systems
- Automating access controls
- Enriching SIEM events
- Enforcing compliance workflows
Core Capabilities
1. Multimodal ITDR
Detects spoofed identities, abnormal behavior, and lateral movement across biometric, behavioral, and risk-based signals.
2. Signal Ingestion and Bridge API
APIs enable standardized ingestion of deepfake, narrative, and media intelligence signals into the security stack
3. SOAR Automation
Automates responses such as:
- Account suspension
- Communication freezes
- Executive impersonation alerts
- Incident escalation
4. SIEM Enrichment
Adds narrative-based indicators to internal logs, improving visibility and reducing alert fatigue.
5. Compliance and Governance Workflows
Triggers audits, regulatory reports, and leadership notifications when trust risks arise .
Collaborative Ecosystem Model
CyberSIO enables an integration-first model where:
- Narrative AI startups plug into enterprise SOCs
- Media intelligence firms route signals securely
- Governments and BFSI respond faster to trust threats
This ecosystem ensures scalability and future readiness.

Adoption and Deployment Model
Organizations typically implement disinformation security in three phases.
Phase 1: Targeted Protection
- Executive monitoring
- Brand and impersonation defense
- Pilot deployments
Phase 2: SOC Integration
- Workflow automation
- SIEM and ITDR correlation
- Incident playbooks
Phase 3: Enterprise Expansion
- Organization-wide coverage
- Predictive analytics
- Advanced attribution
This phased approach accelerates ROI while building long-term maturity.
Preparing for the Future of Influence-Based Threats
As AI continues to advance, enterprises must prepare for:
- Real-time deepfake generation
- Automated social manipulation
- Multi-channel impersonation
- AI-driven fraud networks
CyberSIO’s focus on identity security, signal-to-action translation, and systemic integration positions organizations to defend against these evolving risks
Conclusion
Disinformation security and deepfake detection are no longer optional capabilities, they are foundational to digital trust and enterprise resilience. By embedding narrative intelligence, identity protection, and automated response into core SOC operations, organizations can shift from reactive damage control to proactive risk management.
With its ITDR platform, integration-first architecture, and response-driven security model, CyberSIO enables enterprises and governments to protect not only systems and data, but also identity, reputation, and public confidence.
In an era where trust is the primary attack surface, the future of cybersecurity lies in securing influence, identity, and credibility at scale.